MobyGames turns 20 years old on Friday March 1st, something I am overjoyed to witness. It’s occasion enough for me to come out of semi-retirement and tell my side of the story of MobyGames’ humble beginnings: A tale of two friends starting up a company to fill a void in the gaming community.
MobyGames was created in a figurative basement (an apartment, actually) during the formation of the first Internet Bubble, and somehow stayed alive and grew once that bubble popped. It has become the de-facto source of historical data of the game industry, for people both inside and outside that industry. It is frequently cited as the source of material for tens of thousands of Wikipedia articles on video and computer games. It has achieved and surpassed the goals I originally had for it, and I’m grateful to everyone who volunteers their valuable time to contribute to the database, even more so by all of the admins who edit and audit all of the information for accuracy and authenticity. I am humbled by all of their efforts, past, present, and future.
Before I go any further, I want to make one thing very clear: While I’m writing this article from my perspective as the person who dreamed up MobyGames, the real hero is Brian Hirt. Brian was the other co-founder at our inception, and MobyGames simply wouldn’t exist in any usable form without his many years of dedication getting it off the ground. A lot of people don’t really understand what goes into making a new online product and a company to support it, and it was even harder in the 1990s when the web was still young; there simply weren’t many off-the-shelf components and established standards you could use to jumpstart the process. Brian did just about all of the gruntwork, from establishing the business entity, to writing all the code, to working on MobyGames full-time for many years. Some of those years, Brian didn’t earn a living wage, while still somehow managing to invest a substantial amount of his own money into keeping MobyGames afloat (hardware, rack space, and network bandwidth aren’t free). Everyone who has gleaned use out of MobyGames owes a huge debt to Brian. I, for one, will be eternally grateful to have worked with a good friend who believed in my idea.
I’d also like to thank Rob Lim (cornpopper), who was an early contributor that became such an approval powerhouse that we hired him on as an employee. He took on more than was asked of him, and kept MobyGames data flowing during some of its darker times — a thankless job, but one I do thank him for.
This article is, by necessity, subjective; it’s based on my personal recollection of events. Others may remember events differently; I speak only for myself. Also, I’m not going to write about anything that didn’t go smoothly in MobyGames’ history — I don’t want melodrama to detract from the achievement MobyGames is today. Finally, it’s customary to remind readers that my opinions are my own, and do not represent the current ownership, staff, admins, or contributors of MobyGames.
So, what led to the birth of MobyGames? Now that the statute of limitations has long expired, I can formally confirm that the idea was born out of software piracy. Wait, what? Read on, true believer:
A Software Pirate Reforms
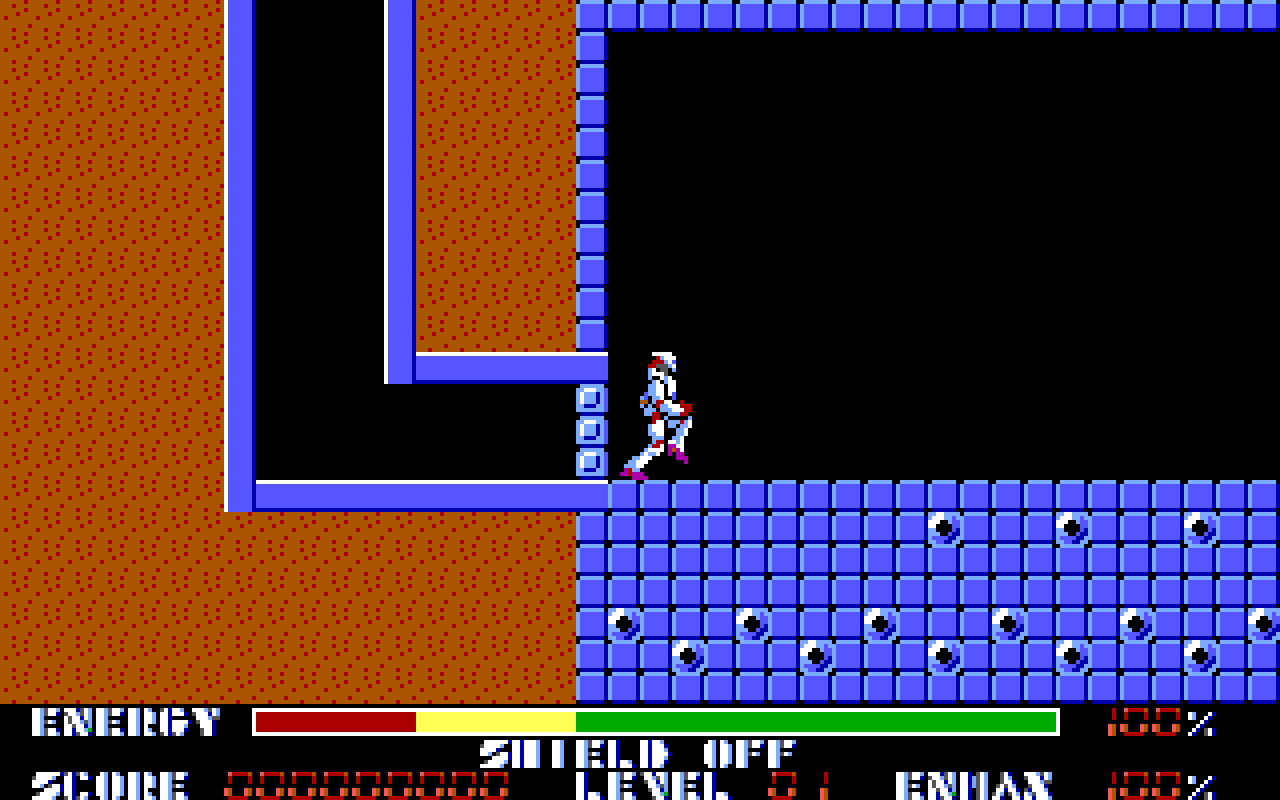
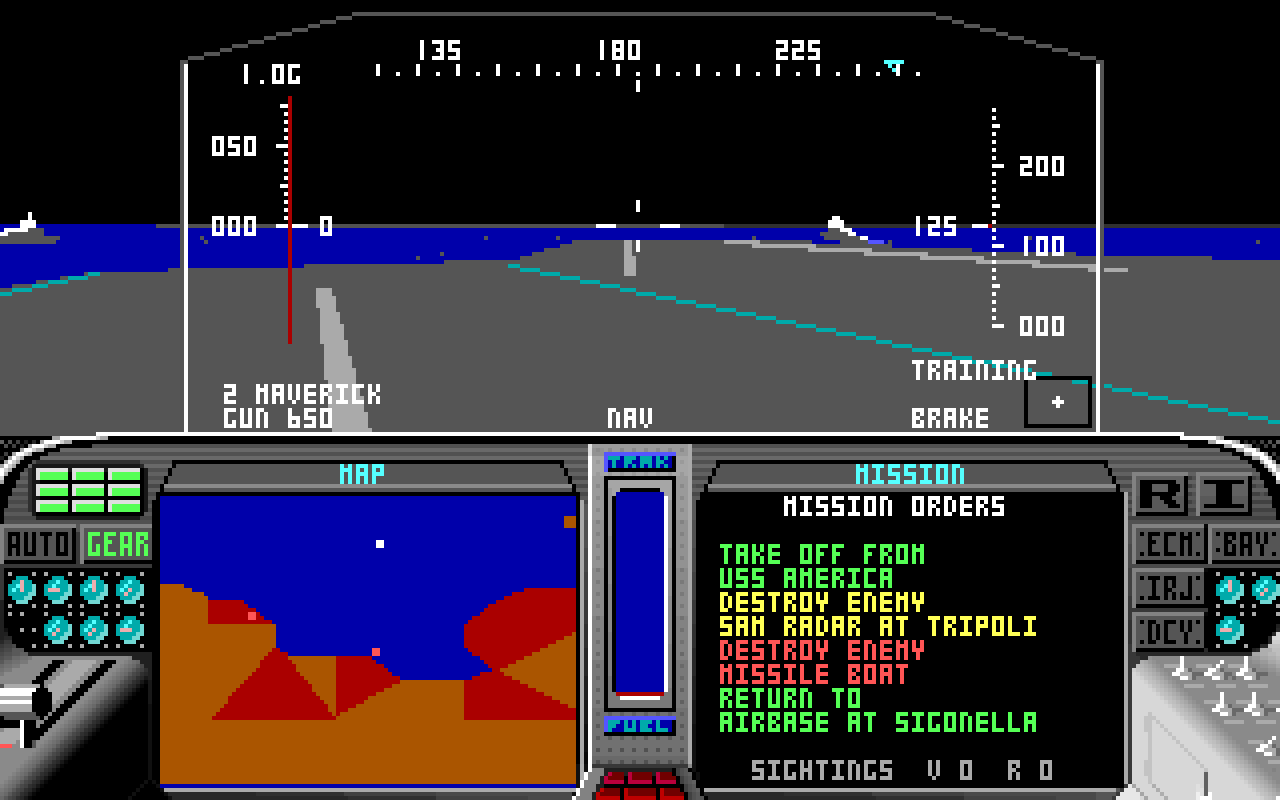
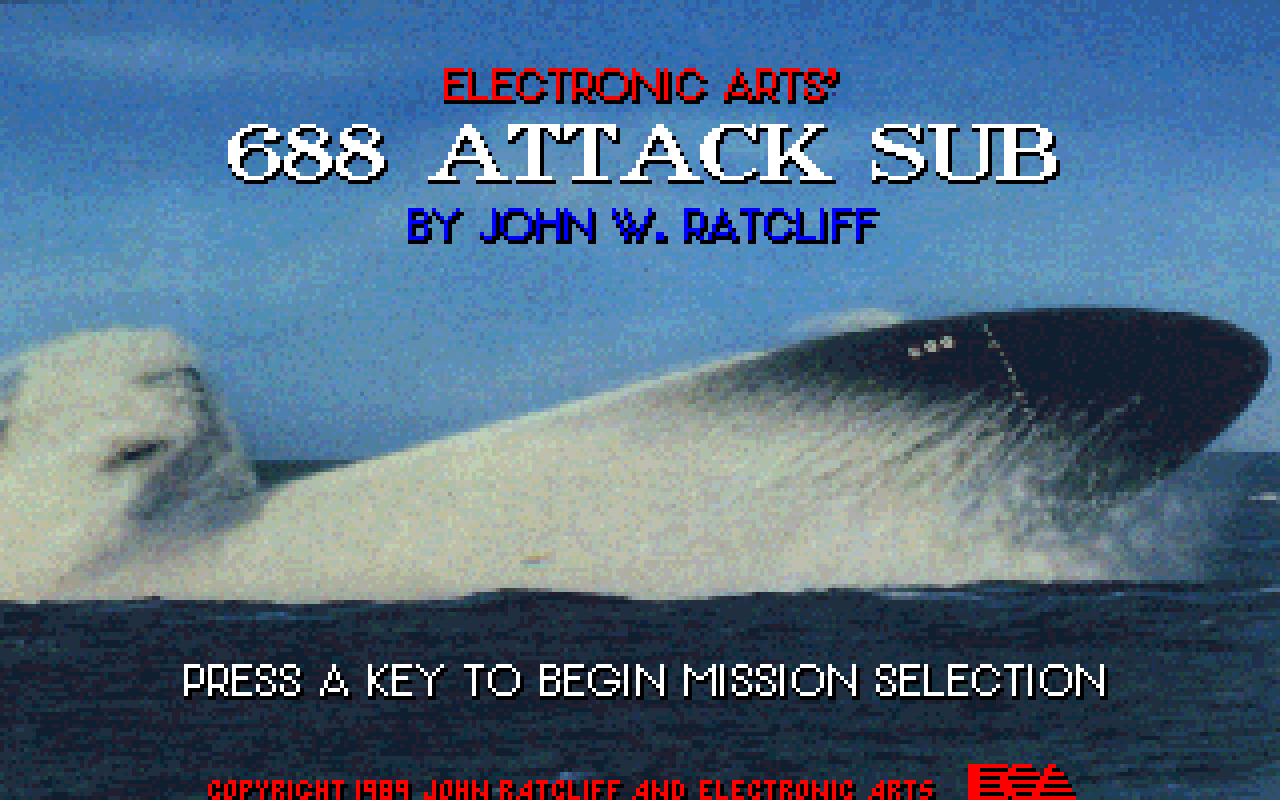
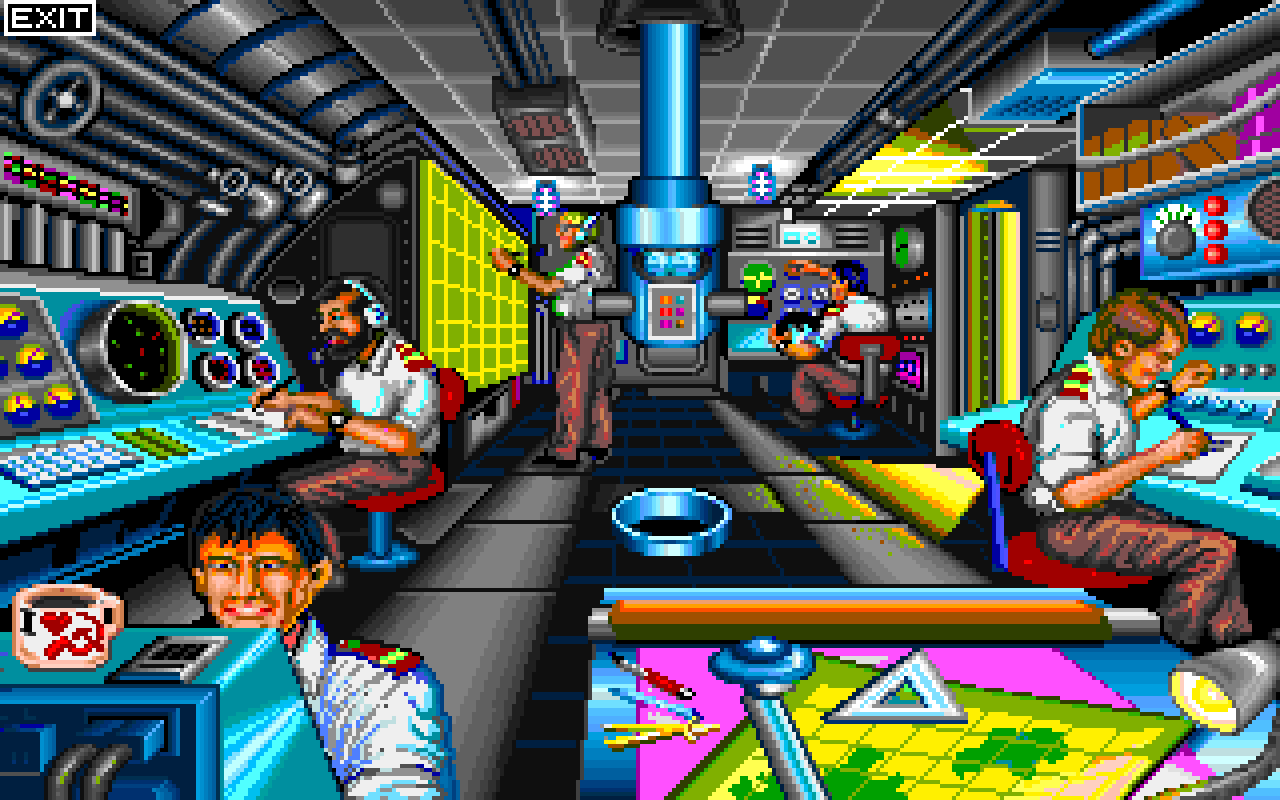
In 1997, I operated a website dedicated to classic games for the IBM PC. (My site was one of the original 10 Abandonware sites that started the Abandonware movement, but that early history warrants its own article for another day.) Why classic games? Early games hold a certain charm for me because they were pioneers of a new art form — interactive electronic entertainment — and the IBM PC fascinated me in particular: A business machine attempting to entertain instead of crunch numbers. While there was no shortage of early console and arcade games before personal computer games, the IBM PC had fairly bad graphics and sound, so creating an immersive entertainment experience on that platform was particularly difficult. I admired any effort to do so, and wanted to share this admiration with the rest of the world, which I did with voluminous amounts of information per game, including what kind of game it was, who made it, other games like it, what it looked like, and a personal review of the gameplay. All of this information was presented in a quasi-database format, with crude searching and organizing capabilities. It was a proto-MobyGames, and, amazingly, you can still view it thanks to the Internet Archive, who was covertly spidering the web for years before offering their archives to the public in 2001.
There was only one problem: What I was doing was illegal. In my quest to educate people on the merits of early IBM PC games, I became overzealous and included download links to the actual games themselves. At the time, I thought that if other people could enjoy them in the same way I had years ago, they would gain a better understanding of the art form. The ESA (back then known as the Interactive Digital Software Association, or IDSA), rightly so, quickly made me aware that what I was doing was illegal with a cease and desist letter sent in October of 1997. Discouraged, I took down the entire site and shelved the idea of documenting the history of early PC gaming.
It was in 1998 that I was motivated to revisit the idea. Fueled by nostalgic curiosity, I had attempted to search for some information on older games that I wanted to play or learn more about, but kept coming up short in all of my searches. I wasn’t being totally unreasonable; I was searching for answers to questions like these:
- Who composed the wonderful AdLib music in Continuum, and what else have they worked on?
- Did that old Cinemaware samurai game ever come out for the PC?
- Everyone on the newsgroups talks about Star Control 2; will it run on this old Tandy I have lying around here?
- Speaking of which, what other games will take advantage of my Tandy’s sound and graphics?
- I like racing games; what other racing games were made for the PC?
- I am completely stuck in Indiana Jones and the Fate of Atlantis; where can I get a hint or walkthrough for older games?
- Speaking of which, what other games are like Indiana Jones and the Fate of Atlantis?
- I’ve never played King’s Quest 7; what does it look like?
I was coming up short again and again, day after day, and I kept thinking that there had to be some place you could go to for answers. Usenet provided information with some quality control (whenever someone posted bad info, someone else corrected them) but the results were partial and scattered. Various websites were a bit more concise, but had absolutely no quality control. While the wiki itself had been invented two years prior in 1995, this was 1997, and Wikipedia wouldn’t launch for another three years. The more I searched, I kept thinking there should be a single, complete, audited resource for gaming information — and eventually, I became determined to create that resource.
In January of 1998, I began work on an extension to my old hobbyist website, http://www.oldskool.org, that would be an online database of gaming information. My website experience at the time was PHP and standard Apache server-side includes and CGI, so I naively thought I could build the entire database out of a quasi-relational database system of my own design using a Perl/PHP mix and text files. (You can stop laughing now.) I brainstormed for a week and created a design document for the project, which is the true original kernel for the design of MobyGames.
Seeing as this design document is the first milestone in MobyGame’s history, I have kept it online for your amusement. While it is mostly humorous to see just how different MobyGames is today from that original design — and how naive I was in thinking that the proposed design could scale to millions of unique IPs per month — it is interesting to see how similar MobyGames today is to the original vision. Even the hacker slang term “Moby” is in that document, as the search function was going to be called MobySearch.
The work involved in programming a custom system of that scale was beyond my capabilities at the time, so I decided to bone up on PHP and Perl to develop the system. However, the entire idea was put on the backburner as I got distracted with real life (new job, newborn son, etc.) It was in December of 1998 that the real surprise came.
“Go here.”
In mid-December 1998, I worked up the courage to begin the gaming database project again. In trying to take a stab at programming the database system, I had run into a lot of problems, and called my longtime friend from high school (and best man at my wedding!) Brian Hirt, a higher-order Perl and SQL god, for advice. I had difficulty explaining the problems I was having, so he asked for a view of the big picture: What was I trying to accomplish? What system was I programming it in? We talked for almost an hour, with me explaining my idea and the motivation behind it, the way I wanted it to navigate, how I wanted it to appeal to the user, etc. and with him asking related questions for clarification. We then talked about other regular stuff, like games, family, etc. and then hung up, and that was the end of it.
About two days later, he called me up and said mysteriously, “Go here,” and gave me a URL to follow. To my utter amazement, it was a mock-up of my idea — and scarier still, it was a functional mock-up! He had already created a basic relational SQL database, and a basic web front-end to browse through the database. My jaw hit the floor. It was the fastest, most functional prototyping I have ever witnessed, but equally surprising and wonderful was that Brian was very excited in the idea and wanted to co-develop it with me.
The next six weeks were a blur as Brian and I went back and forth over email and the phone, working out the basic structure and navigation. The original idea was to develop in PHP shelling out to SQL for the data, so that I could help develop it, but early on Brian did some scalability tests that showed PHP was not up to the task of scaling properly. (This was before the days of Zend, p-code, and JIT compilers.) In early February of 1999, the development system of Apache serving up a large monolithic Perl program was finalized, and we refined what we wanted MobyGames to be. Finally, a few days before March 1st, Brian added the first game ever to the database: X-Files. And on March 1st, I started posting to Usenet announcing the grand opening of MobyGames.
Open for Business
It is at this point you would expect me to say “and the rest is history” — but in fact, things were only just starting to heat up. The entire month of March 1999 had Brian and me exhausting all of our free time entering games into the database, and fielding email containing new database submissions and corrections. By the end of March 1999, there were over 200 games in the system; some strategically chosen to exploit the database engine’s ability to cross-link from entry to entry, and others chosen simply because they were our favorite games. I was personally spending at least 3 hours a night entering information into MobyGames — entering data, scanning covers, playing the game to take screenshots and write a review, etc. — and it simply wasn’t growing fast enough. I was initially resistant to the idea of opening up MobyGames to outside contributors because I wanted to control the quality of the information in the database. Brian had to convince me, over many weeks, that it was painfully obvious we needed a way for willing users to help out without our direct intervention.
(I should take a moment and point out that all the scanning, screenshots, etc. may have seemed like unnecessary work in getting MobyGames off the ground — just get the basic data in there, right? But they were necessary, because the whole point of MobyGames was quality over quantity. Sure, we could have just scraped the Killer List of Videogames, or Dadgum’s Giant List of Classic Game Programmers, but we would then have a database that was a mile wide and an inch deep. There’s no value in looking up a game only to see four or five things about it, barely confirming its existence. There were (and still are!) databases like that out there, like the Universal Videogames List, but it is the depth of information about each game and attention to detail that makes MobyGames the resource that it is today.)
Much of the time Brian spent on development in the first six months of MobyGames’ existence was developing a way for users to submit information for review and inclusion into the database. Brian had the idea of walking the user through the process, allowing them to contribute anything they wanted yet still requiring a few key pieces of information like title, developer, publisher, release information, genre, description, and rating categories. He came up with a practical method of doing this, virtually holding the user’s hand through the process and allowing them to go back and correct mistakes before submission. The benefit to the database was that it ensured the data was normalized and conformed before it was comitted. This became the Add Game Wizard, which is still in use today.
Along with the wizard, a method of motivation was needed to help entice people to contribute to the project, and help existing contributors continue adding information. Enter human psychology: Earlier in life, I’d contemplated going into marketing and advertising, and for a year I took classes to that effect. While I didn’t follow through with that as a career path, I did take away some basic knowledge that I applied to MobyGames. I came up with a point system for contributors: 4 points for an entry, 2 points for a screenshot, etc. The more you contributed, the more “contribution points” you got, and that number was proudly displayed next to your name, which itself was displayed on the same page as the information you contributed. This made MobyGames, itself, a game: You could watch your own progress grow, and also identify other users just as passionate as you. It was an early form of website gamificiation, years before Nick Pelling coined the term in 2003.
The earliest browsable archive of MobyGames available online is from around this time that same year (November, 1999). I haven’t seen that form of the site in nearly two decades, but even at that early stage, I’m reminded of how useful it was even before it was a year old.
Opening the Gates
The Game Wizard was a success, but it was a blessing in disguise: We found ourselves under a steadily increasing load of approvals instead of content entry. Approval of an entry is not something to be taken lightly; it may need to be fact-checked using whatever resources you have available to you (old game lists or magazines, the web, Usenet, game binary code or manuals, etc.). Even if we could approve about half of the entries without any research because of our strong backgrounds in gaming, it still left the other half to research. We found ourselves getting overwhelmed.
Luckily for us, we had struck up email dialogs with ten or so dedicated users who were friendly, prolific contributors. They had expressed a desire to help, so Brian got to work on a hierarchial approval system, where people could “weed out” the easy approvals and send only the harder ones up to us. This system worked so well that we felt it was time to open up the floodgates to multiple platforms.
Multiple platforms? Yes, for the first two years of MobyGames’ operation, our sole coverage of games was on the IBM PC platform. This limitation seems unfathomable, but was actually my fault. I was very much against multiple platforms from the beginning, because I wanted to ensure quality of submitted information, and I felt limiting to the DOS/Windows platforms was the best way to do that because it was the platform Brian and I were the most familiar with. Brian wanted multiple platform support from day one, and being limited to DOS/Windows for the first two years was something we frequently clashed over. It took a third informed opinion from someone else before I finally realized the value of covering the entire electronic entertainment landscape. It’s one of a few things I regret about how I handled MobyGames’ development and growth.
With an approval system in place and users manning the content entry battlements, we started adding platforms. The first choice for new platforms was (then) modern consoles: PlayStation, PlayStation 2, Nintendo 64, Xbox, Dreamcast, and Game Cube. Adding only the latest platforms at the time was intentional, to ensure a large, growing library of games to be added, which had a secondary benefit of working out kinks in the new system.
Keeping Up Appearances
We figured out early on that the data in the database was the way for MobyGames to grow in value, and growing in value meant more visitors, more advertising revenue, and more opportunities to turn MobyGames into a full-time business for all involved. To that end, we printed up promotional materials and manned booths at several events, to spread the good word. The largest three I personally attended were:
Classic Gaming Expo 2003, August 9–10, Las Vegas, Plaza Hotel: This was my first time in Las Vegas, and while that experience was somewhat overwhelming, the actual show and manning our booth was a blast. We got nothing but great comments and feedback, which was vindication of our work and idea. One of the problems of trying to promote an internet-only business in 2003 was lack of internet connectivity — whole-event wireless was not yet a thing, and they couldn’t run cables to every table, so how do you show off a site on the internet if you have neither? Brian solved this by working up a portable version of MobyGames we dubbed PortaMoby(tm), displayed on a custom-milled aluminum stand.
Classic Gaming Expo 2004, August 21–22, San Jose, McEnery Convention Center: For the much-larger CGE2004, we had a double-size booth area, and set up both a gaming lounge as well as a projector showing off a trivia game that you could find the answers to on PortaMoby: Play the game and we gave you a free soda; get all the answers right and earn a T-shirt. For more details of what it was like, you can consult the blurb I wrote about CGE2004 at the time. Better yet, you can skip right to our booth footage at the 4m40s mark in this video retrospective I shot and edited in 2004:
Game Developer’s Conference 2007, San Francisco, Moscone Center: I developed a 103-degree fever right when I arrived on Monday that lasted for 3 days. I don’t have a consistent memory of that week, but can recall a few notable (for me) events:
- People kept coming up to the booth and asking us what we were doing there. I was confused by this at first, thinking it was a put-down or an insult, but it turned out to be a gigantic complement — everyone in the gaming industry already knew about us. In other words, there was no need to advertise MobyGames because it was already an established resource for the professional gaming industry. It was a huge moment of validation.
- I am video compression nerd, and when I realized RAD Game Tools was only a few booths away, I stole some time to talk to Jeff Roberts and tell him what an admirer I was of both Smacker and Bink. He was impressed I had reverse-engineered parts of them, but then laughed because Bink was constantly changing for new platforms and there was no way reverse-engineering Bink was viable year after year. (He was right!)
- On the Wednesday night awards show, we were seated at the intersection of two walkway rows. After accepting an award, Shigeru Miyamoto headed back to his seat, and he chose the walkway closest to where we were seated. He got so close that Chris, an intern working for MobyGames at the time, stood up and got him to shake our hands. In hindsight, I probably shouldn’t have shaken hands with someone when I had a 103-degree fever, but hey. Chance of a lifetime.
- On Thursday morning, I felt well enough to attend the IGDA Game Preservation SIG’s kickoff meeting, also on the premises, and met Henry Lowood and Frank Cifaldi during the roundtable discussion. Henry and I have written sporadically a few times over the years, and I reconnected with Frank in 2021 via Twitter.
Regrets? I have a few
A lot of people have asked me over the years why I didn’t stay active with MobyGames. The first two years, I put every single hour of free time I had — and several day job hours, something my employer never found out about — into the site. By 2001, I had two young boys, one of whom was developing some very severe developmental delays. My wife was overwhelmed; I had been neglecting the family a lot during that time, and she needed help with our son who was starting special therapy and undergoing a battery of tests. I was the sole wage earner, and MobyGames didn’t make money its first few years, so I couldn’t make it my full-time job. I started to pull back my involvement, and only dedicate truly free time to MobyGames (ie. after everyone was in bed), which amounted to about 60-90 minutes per evening, with a few hours on weekends. This had a detrimental effect on Brian’s ability to support the site, because he had to take on additional community manager and approval duties that I had mostly owned. Thankfully, we had additional professional interest in the site at that time, who joined on and was able to help as I spent less and less time on MobyGames.
Because of pulling back, I never had the chance to help Brian code up one of my most ambitious goals for MobyGames: Discovery based on a pure gaming taxonomy. I wanted MobyGames to be the ultimate game discovery engine, and my idea for achieving that was to define a very clear gaming taxonomy/heirarchy that every game could be classified under. That structure is somewhat intact even today; if you go to the Game Browser, you can see some top-level classifications like Genre (Action, Sports, Adventure, etc.), with sub-genres and additional branches of the taxonomy, perspective in particular (top-down, 1st-person, etc.). One of the ideas behind the discovery engine was that you could pull up a game you liked, and based on its individual components, could recommend other games that were similar. For example, let’s say you pulled up Ultima 6. Based on “Adventure”, “Role-playing”, “top-down perspective”, “DOS”, etc., the engine could return the results of a database query that would show you similar games. Of course the other Ultima games would be returned by such a query, but also games like Wasteland, Times of Lore, Hard Nova… other games that share the same classification attributes, but possibly in completely different story settings, possibly some you’d never considered before. The Game Browser, as well as the Collaborations area of any Credits section, come closest to this vision today.
I didn’t communicate this taxonomy idea very well with the broader MobyGames community, which is why I fought against a 2006 vote to create Role-Playing as a main, top-level genre in the database. My argument was that all RPGs were Adventure-class games, which is technically true, but not a view shared by most gamers due to unfamiliarity with what I was trying to achieve, as well as the changing nature of language. I was faced with sticking to my guns in support of a pure taxonomy while alienating many valued members of the contributing community… or letting go of the idea to keep the community together. I chose the latter, but it was a blow to my ego that contributed to me pulling away from MobyGames even further. By 2007, I was technically still a partial owner of the company, but I wasn’t involved in the day-to-day running and administration of MobyGames any more.
I regret how I handled some of these situations. My home life was turbulent at the time (my son was eventually diagnosed with autism, and things only got harder after that), but even still, I could have found better ways to communicate and at least stay in the loop, rather than just fading out.
Legacy
Remember those questions I was trying to answer back in 1998? MobyGames can easily answer them now:
- Who composed the wonderful AdLib music in Continuum, and what else have they worked on? Frédéric Mentzen, and he stopped writing game music shortly after MobyGames was founded.
- Did that old Cinemaware samurai game ever come out for the PC? Nope!
- Everyone on the newsgroups talks about Star Control 2; will it run on this old Tandy I have lying around here? Not unless it has an 80286 and VGA, no.
- Speaking of which, what other games will take advantage of my Tandy’s sound and graphics? Over 800!
- I like racing games; what other racing games were made for the PC? For DOS? Over 250.
- I am completely stuck in Indiana Jones and the Fate of Atlantis; where can I get a hint or walkthrough for older games? While gamefaqs cornered the market for walkthroughs, we implemented basic hints that users could contribute.
- Speaking of which, what other games are like Indiana Jones and the Fate of Atlantis? Whether you meant like Indiana Jones or like SCUMM games, MobyGames has groups for both.
- I’ve never played King’s Quest 7; what does it look like? Like a cheap cartoon, unfortunately.
Some of the more fun stuff include questions that I couldn’t dream of answering back then that I can now, like:
- I really liked Wasteland; what other games did those guys make?
- Tass Times in Tonetown is one bizarre game! Is there any bizarre trivia to go with it?
- Just how many different platforms was Dig Dug released on? (As of today, 34 and counting)
And so it goes. And in the capable hands of the current owners, with all of the tireless efforts of dedicated admins and contributors, I look forward to another 20 years using MobyGames.
5th-year Anniversary Testimonials
Portions of this article were originally written in 2004 for an unpublished piece praising MobyGames’ 5th-year anniversary. At that time, I solicited some comments and testimonials from various users of the site as well as industry professionals, and am happy to finally reproduce them here:
“MobyGames has developed its content so professionally that it’s an invaluable source of information on dates, companies and people. I particularly find the cross-referencing of information incredibly useful — finding out what games certain people have worked on throughout their careers. It’s the IMDB of the PC gaming industry — a site that every gamer should have bookmarked.” — Rob Smith, Editor-in-Chief of PC Gamer magazine
“Imagine my surprise and astonishment when I stumbled upon mobygames a year or two ago… here was a system that was working to catalog games! Not just release information (still more than I had done already) but also interesting things to set any one game apart from all the others… things like trivia, screenshots and it’s cover art. A magic spark went off inside my head because here was something that someone else had dreamed up that was suspiciously similiar to my own dreams and disjointed design scribbles on notepaper…” — WildKard
“Its shining glory .. compiling data about game developers and their roles. Nowhere else on the internet can you find that. Movie and theater cast members … but never for games.” — Jeanne
“There are many sites with plenty of information about games, but none of them can even be compared to MobyGames, for two main reasons: Scope and personal involvement. No other game catalogue website allows the user an unlimited involvement in its development, together with countless other contributors. The feeling of growth and of challenge — so many games are still not documented, so many entries are still incomplete, what about finding some rare games to add, screenshots that are tricky to capture, credits that are not documented anywhere except in the game itself, interesting trivia, personal and involving reviews? — is one of those things that make MobyGames so great.” — Unicorn-Lynx
Random Trivia
- The first month of MobyGames’ existence, it lived on a 200 MHz Pentium II server in Brian’s apartment, and was connected to the internet via a 128K ISDN line.
- The first game ever entered into MobyGames was The X-Files Game. This was not because it was a great game, but rather because Brian was testing the system and it was the first game within arm’s reach. The second entry was by myself, for Who Framed Roger Rabbit?. It was, also, the closest game within arm’s reach for me; I’d grabbed a smattering of titles from my collection to start populating the database with. The third entry was more proper for a historical database on gaming: Wing Commander. (As of today, these last two entries still retains their original contribution date of March 1st, 1999.)
- The first developer entry fleshed out with a Bio and picture was Michael Berlyn.
- In the 1990s and early 2000s, whenever someone on a Usenet binary piracy newsgroup wanted to refer to a game without giving away its title, it was common to see the game represented as “gameId,11970”. This is a reference to the game ID embedded in the URL of early game entry “Rap Sheets” (summary pages) on MobyGames.
- One of the earliest funny and most blunt developer-contributed pieces of trivia would have to be John Romero’s recounting of why the low-res graphics mode was present in Doom but omitted in Doom II: “160-pixels horizontally looked like ass so we removed it.” This trivia item is no longer in the database for some reason, but I’ll never forget it.
- California Games’ gallery of screenshots for DOS contain a few shots called “CGA ‘MORE-color’ mode” that are technically impossible to capture by dumping the screen buffer on the original system, because the additional colors were created with realtime scanline tricks. The screenshots in MobyGames that depict this mode were hand-edited to match the original graphics mode, and were matched side-by-side with an original IBM PC for authenticity. Today, in 2019, both emulators and homebrew TTL-to-RGB converters make it possible to capture more true CGA output regarless of what tricks were used, but back then we had to massage the raw screen dumps/captures for tweaked modes like this. I even wrote a screen-capture TSR to help contributors take shots of the more difficult and odd CGA DOS games.




You must be logged in to post a comment.